Blog Posts
Home
Critical Nginx UI Flaw Exposes Web Application Security to Full Takeover
The digital perimeter of modern enterprises is constantly under siege,…
OpenAI Trusted Partners Gain Exclusive Access to GPT-5.4-Cyber
The dawn of advanced AI models capable of autonomously identifying…
Oracle Cloud Infrastructure Elevates AI Database with 26ai, New Compute,…
The relentless pace of innovation in artificial intelligence is fundamentally…
Critical Docker Security Vulnerability: CVE-2026-34040 Threatens Host Sy…
The Silent Threat: Docker's Authorization Bypass (CVE-2026-34040) In the rapidly…
AI & Legacy Contact Centers: TTEC Digital’s AI Gateway Rewrites Integration
The relentless pace of AI innovation is both a beacon…
NIST Unveils OpenLQM & Annotated SD 302: A New Era for Fingerprint Foren…
In the high-stakes world of forensic science, the reliability and…
WordPress 7.0 Delayed: Architecting Collaboration, Mitigating Critical R…
The Imperative of Adaptability: Navigating WordPress 7.0's Delay and Escalating…
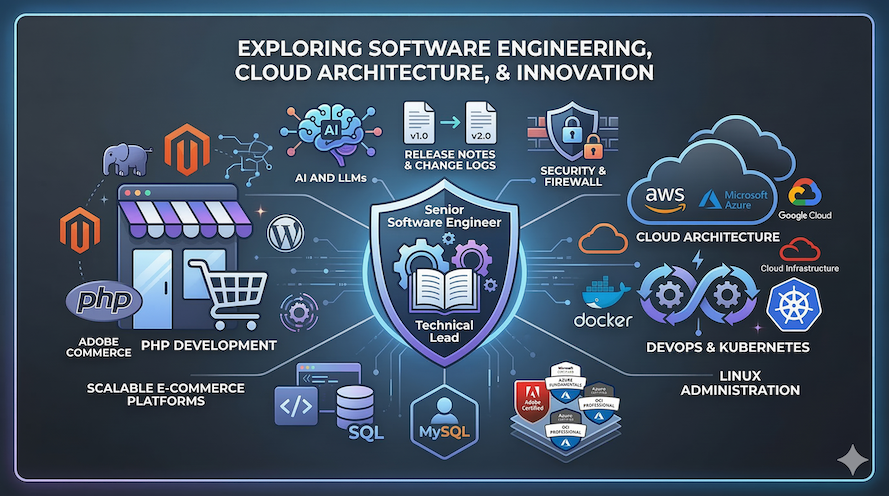
Magento 2.4.9: Critical Upgrade Imperative for Security & Performance
The digital commerce landscape is in constant flux, but few…
Flatiron Software Releases Open Source AI Summarization WordPress Widget
The landscape of content management is undergoing a profound transformation,…
Ubuntu 24.04 LTS: Noble Numbat Redefines Enterprise Linux Security
In the dynamic landscape of enterprise IT, maintaining a secure,…