Archive Post
Home|Cybersecurity
Google Chrome’s Stealthy Gemini Nano Download Sparks Privacy Concerns
Google Chrome's Silent Gemini Nano Download Raises Alarms for 3…
Project Glasswing: AI’s Leap in Software Security or a New Threat?
The AI-Powered Arms Race in Software Security: An Urgent Call…
AI Models: Mythos, GPT-5.5, and the New Cyber Frontier
The AI Tsunami: Mythos and GPT-5.5 Redefine the Threat Landscape…
Log4j: The Persistent Threat of Supply Chain Vulnerabilities
Log4Shell: A Lingering Shadow in the Software Supply Chain In…
Web App Security: 2026 OWASP Top 10 and Emerging Threats
The Unchanging Landscape: Why 2026 OWASP Top 10 Still Features…
Cloudflare’s Accelerated Post-Quantum Shift: Urgent Implications for Eng…
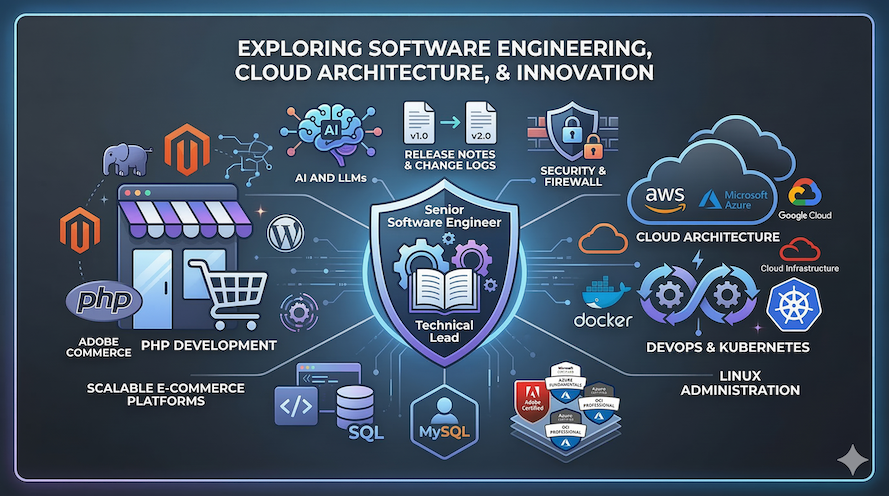
The cybersecurity landscape is experiencing a paradigm shift, driven by…
Anthropic Claude Mythos AI Model Withheld: A Cybersecurity Imperative
The artificial intelligence landscape is evolving at an unprecedented pace,…
Anthropic Mythos: The AI Model Redefining Cybersecurity Urgency
The ground beneath the cybersecurity world has undeniably shifted. A…
OpenClaw 2026.4.29: Urgent Security Patches & Autonomous AI Evolution
The landscape of autonomous AI agents is evolving at an…
Critical Cybersecurity Vulnerability in .NET EncryptedXml Demands Immedi…
The digital landscape is a relentless battleground, and for R&D…