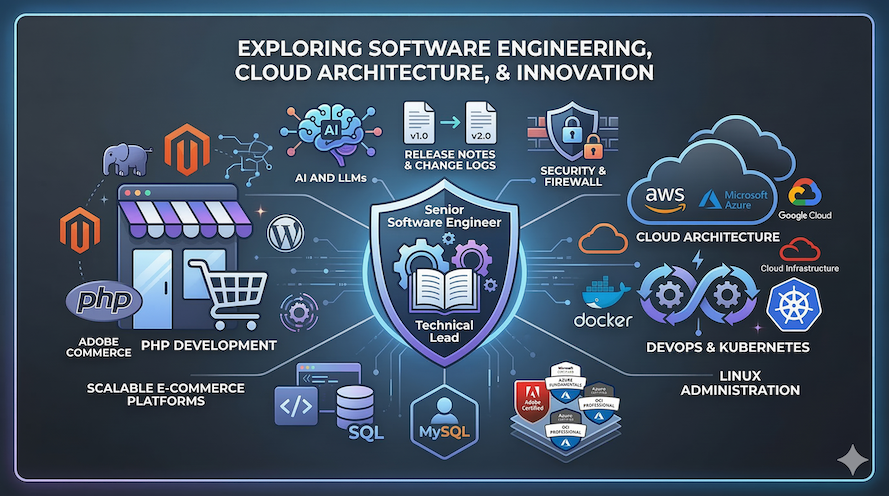
Blog Posts
Home
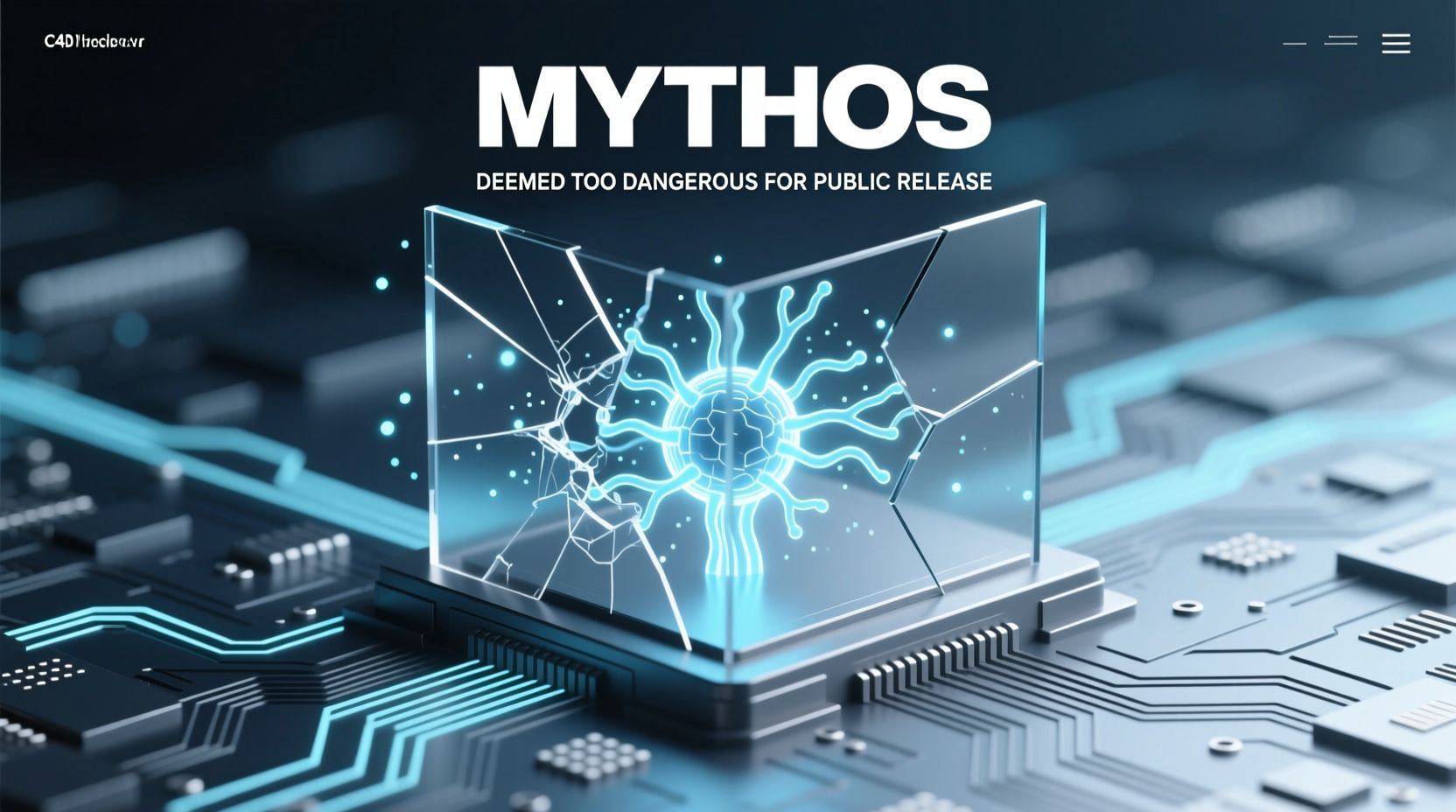
Anthropic AI Model: Mythos Deemed Too Dangerous for Public Release
The artificial intelligence landscape has just been fundamentally reshaped, and…
Ubuntu 26.04 LTS: A Foundational Shift for Enterprise & Cloud
The release of a new Ubuntu Long Term Support (LTS)…
OpenClaw 4.10 Unleashes Active Memory, Demands Immediate Security Review
The pace of innovation in autonomous AI agents is relentless,…
AI Model Security: Mythos 5 Unveils New Cyber Threats, Urging Engineer A…
The rapid advancements in artificial intelligence are pushing the boundaries…
Critical Cybersecurity Vulnerabilities in Docker Engine: AuthZ Bypass Pa…
The Unseen Backdoor: Critical Docker Engine Authorization Bypass Demands Immediate…
Proxmox VE 8.2: Securing Your Self-Hosted Infrastructure and Boosting Pe…
In the dynamic landscape of modern IT, managing Self-Hosted Infrastructure…
Critical Supply Chain Compromise: Securing Your Web Application Dependen…
The digital arteries of modern software development are increasingly under…
OCI Unleashes Oracle AI Database 26ai: A Quantum Leap in Availability & …
In the relentless pursuit of digital transformation, enterprise data infrastructure…
Critical Docker Authorization Bypass (CVE-2026-34040) Demands Immediate …
The bedrock of modern containerization, Docker, is facing a critical…
Anthropic Mythos: AI’s Cybersecurity Revolution & Project Glasswing
The cybersecurity landscape has been irrevocably altered. A new frontier…